
Photo by Jefferson Santos on Unsplash
A Journey into Cybersecurity: A Student's Perspective
Introduction
Table of contents
- Let us explore some technical stuff in this field together
- Security
- Cyberthreats
- Types of Cyber Threats
- Cyber attack techniques
- Phases of Hacking
- Introduction to Cryptography
- Key terms:
- Symmetric cryptography:
- Asymmetric cryptography/Public key cryptography:
- Block Cipher:
- Stream cipher:
- Digital Signatures:
- Hash Algorithms:
- Malware Analysis
- Stages of Malware Analysis
- Tools for Malware Analysis
- Linux
- Basics of Networking
- Fields in Cybersecurity
- Common Cybersecurity Certifications
- Why learn Cybersecurity?
- Conclusion
As a student studying cybersecurity, I've had the opportunity to learn about the various threats facing businesses and organizations today, and the various tools and techniques used to protect against them. It's been a fascinating and rewarding journey, and I wanted to share some of my experiences with others who might be considering a career in this field.
When I was allotted a project under Celestial Biscuit, this was the time I started studying cybersecurity, I was intimidated by the complexity of the subject. There seemed to be so much to learn, and I wasn't sure where to start. But as I progressed, I began to see the big picture and how all the different pieces fit together. I learned about topics such as network security, cryptography, OWASP, malware, and cyber threats, and I gained hands-on experience working with tools like Red Hawk, Nmap, WPScan, Aircrack-ng, etc.
Let us explore some technical stuff in this field together
Security
When you hear the word owasp, what do you think it is about? Not Clear, what is it about? Let me narrow it down. "Web application security", What words capture your mind when you think about it? Threats, security, techniques, etc, etc.

Do you want to know more about it?
OWASP stands for Open Web Application Security Project. It is a non-profit foundation that works towards improving the security of the Application or the Software. OWASP foundation is supported by the community that involves open-source projects led by tech volunteers, contributors, and developers. They often conduct educational and training conferences that are helpful for technologists and developers in securing the web and their applications.
OWASP top 10 is the list of top 10 web/software security vulnerabilities that the community of developers agrees in common as per the severities. The list can be referred to take proactive actions against the dangerous exploitations and provides for the appropriate remediations to be followed to deal with them. OWASP has the compilations of all the data about the common vulnerabilities and the surveys from the developers on the same. The top 10 OWASP list was first published in the year 2003. And the updates were followed in the years 2004, 2007, 2010, 2013, and 2017. The most recent OWASP top 10 list was published in 2021.

What are the rules or standards of OWASP?
- Broken Access Control:
Broken access control vulnerabilities exist when a user can access some resource or perform some action that they are not supposed to be able to access.
For example, a web application might have an admin page, but there is no link to the admin page on other parts of the website, a regular user won't find the admin page by simply clicking around.
- Cryptographic Failures:
A cryptographic failure is a critical web application security vulnerability that exposes sensitive application data on a weak or non-existent cryptographic algorithm. Those can be passwords, patient health records, business secrets, credit card information, email addresses, or other personal user information.
- Injection:
An injection is an attacker's attempt to send data to an application in a way that will change the meaning of commands being sent to an interpreter.
An attacker uses the injection to introduce (or "inject") code into a vulnerable computer program and change the course of execution. The result of successful code injection can be disastrous, for example, by allowing computer viruses or computer worms to propagate.
- Insecure Design:
Insecure design is the lack of security controls integrated into the application throughout the development cycle. This can have wide-ranging and deep-rooted security consequences as the application itself are not designed with security in mind.
- Security Misconfiguration:
This vulnerability will occur when a web component is suspectable to attack due to misconfiguration or insecure misconfiguration.
These misconfigurations are in software components or in user administration. For example, if we use default passwords for the system, it may allow attackers to gain unauthorized access to the system.
- Vulnerable and Outdated Components:
It refers to when the open-source code has software vulnerabilities or is no longer maintained. This code can include Libraries, frameworks, etc.
If we don't provide the security patch to the software component that is vulnerable to attack.
- Identification and Authentication Failures:
Identification and authentication failures can occur when functions related to a user's identity, authentication, or session management are not implemented correctly or not adequately protected by an application.
Four types of authentication can be used to prevent data breaches:
1. Password-based authentication
2. Multi-factor authentication
3. Token Authentication
4. Biometric Authentication.
- Software and Data Integrity Failures:
Software and data integrity failures relate to code and infrastructure that do not protect against integrity violations. An example of this is where an application relies upon plugins, libraries, or modules from untrusted sources, repositories, and content delivery networks (CDNs).
- Security Logging and Monitoring Failures:
Failure to sufficient log, monitor, or report security events, such as login attempts, makes suspicious behavior challenging to detect and significantly raises the likelihood that an attacker can successfully exploit your application.
Logging and monitoring will help you to identify patterns of activity on your networks, which in turn provide indicators of compromise. In the event of incidents, logging data can help to more effectively identify the source and the extent of the settlement.
- Server-Side Request Forgery:
Cross-Site Request Forgery is an attack that forces an end user to execute unwanted actions on a web application where they're currently authenticated.
Cyberthreats

Anything with the potential to cause serious harm to a computer system, network, or other digital assets of an organization or individual is a cyber threat. According to Techopedia, cyber threats look to turn potential vulnerabilities into real attacks on systems and networks. Cyber threats include a wide range of attacks ranging from data breaches to computer viruses, denial of service, and numerous other attack vectors. Cybersecurity threats can include everything from trojans, viruses, and hackers, to back doors. Most of the time, the term ‘blended cyber threat’ is more appropriate, as a single threat may involve multiple exploits. For instance, a hacker may use a phishing attack to get information and break into the network.
Together, cyber threat management, cyber threat intelligence, and threat hunting teams form a powerful trio to address the overall cybersecurity needs of global enterprises operating today.
Types of Cyber Threats
Cybersecurity threats are ever-evolving in nature. Enterprise security teams need to constantly stay aware of and ahead of all the new threats in the domain that may impact their business. Here’s a list of common cyber threats that organizations face most frequently.
Malware is an umbrella term that describes any program or file that intends to disrupt or harm a system or computer. Malware breaches a network via a vulnerability, usually when the user clicks an email attachment or dangerous link that installs risky software. The various types of malware software include:
A trojan is a form of malware that disguises itself as legitimate software but performs malicious activity when executed.
Viruses and worms are a piece of malicious code that is installed without the user’s knowledge. These viruses can replicate and spread to other systems by simply attaching themselves to the computer files. Worms are also self-replicating, just like viruses, but they do not need to get attached to another program to replicate.
Ransomware is a type of malware that encrypts a victim’s information and demands payment in return for the decryption key. Even if you pay the ransom, it does not necessarily guarantee that you can recover the encrypted data.
Botnet software is specially designed to infect huge numbers of devices connected via the internet. Few botnets comprise millions of compromised machines, with each using a negligible amount of processing power. This makes it extremely challenging to detect the botnets, even when they are running.
Spyware is a form of malware used to monitor a user’s computer activity illicitly and harvest personal information.
Remote-access Trojans or RATs install backdoors on the targeted systems. They provide remote access as well as administrative control to malicious users.
Backdoors allow remote access to systems and computers without the users’ knowledge.
Domain name system (DNS) poisoning attacks compromise the DNS to redirect web traffic to malicious sites. These do not hack the affected sites.
Distributed denial-of-service or DDoS attacks flood servers, systems, and networks with web traffic to exhaust resources or bandwidth and cause them to crash. Due to this, the system is unable to fulfill any legitimate requests.
In form jacking, malicious JavaScript code is inserted into online payment forms to harvest customers’ card details.
Cyber attack techniques
While many types of cyber attacks are possible, typical adversary attack techniques and tactics can be grouped within a matrix that includes the following categories:
Initial access includes techniques used to attain a foothold within a network, like targeted spear phishing, configuration weaknesses in public-facing systems, or exploiting vulnerabilities.
Command and control involve techniques leveraged by attackers to communicate with a system under their control. For example, an attacker communicates with a system over high-numbered or uncommon ports to evade detection by proxies/security appliances.
The collection includes tactics used by adversaries to gather and consolidate the information they were targeting as a part of their goals.
Persistence includes techniques that enable an adversary to maintain access to the target system, even following credential changes and reboots. For example, an attacker creates a scheduled task that runs their code on reboot or at a specific time.
Defense evasion includes techniques used by attackers to avoid detection. These include hiding malicious code within trusted folders and processes, disabling the security software, or obfuscating adversary code.
Execution involves techniques deployed to run code on a target system. For instance, an attacker running a PowerShell script to download additional attacker tools or scan other systems.
Discovery includes techniques used by attackers to gain information about networks and systems that they are looking to use for their tactical advantage.
Credential access includes techniques deployed on networks and systems to steal usernames and credentials for reuse.
Impact includes techniques leveraged by attackers to impact the availability of data, systems, and networks. It includes denial-of-service attacks, and data, or disk-wiping software.
Lateral movement involves tactics to enable attackers to move from one system to another within a network. Some common techniques include abuse of remote desktop protocol or pass-the-hash methods of authenticating users.
Exfiltration includes tactics utilized to move data from a compromised network to a system or network that’s under the attacker’s complete control.
Privilege escalation involves techniques utilized by adversaries to gain high-level privileges on a system like a root or local admin.
Phases of Hacking
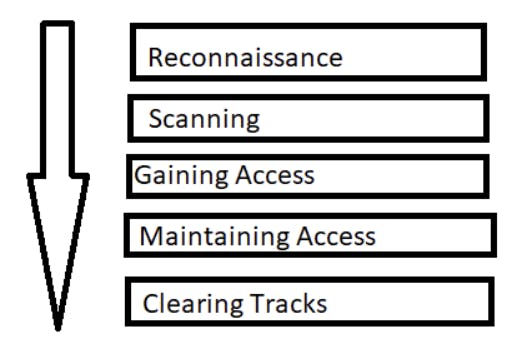
There are mainly 5 phases in hacking. Not necessarily a hacker has to follow these 5 steps in a sequential manner. It’s a stepwise process and when followed yields a better result.
- Reconnaissance:
This is the first step of Hacking. It is also called as Footprinting and information-gathering Phase. This is the preparatory phase where we collect as much information as possible about the target. We usually collect information about three groups,
Network
Host
People involved
There are two types of Footprinting:
Active: Directly interacting with the target to gather information about the target. Eg Using the Nmap tool to scan the target
Passive: Trying to collect information about the target without directly accessing the target. This involves collecting information from social media, public websites, etc.
- Scanning:
Three types of scanning are involved:
Port scanning: This phase involves scanning the target for information like open ports, Live systems, and various services running on the host.
Vulnerability Scanning: Checking the target for weaknesses or vulnerabilities which can be exploited. Usually done with help of automated tools
Network Mapping: Finding the topology of the network, routers, firewalls servers if any, and host information and drawing a network diagram with the available information. This map may serve as a valuable piece of information throughout the haking process.
- Gaining Access:
This phase is where an attacker breaks into the system/network using various tools or methods. After entering into a system, he has to increase his privilege to the administrator level so he can install an application he needs or modify data or hide data.
- Maintaining Access:
Hacker may just hack the system to show it was vulnerable or they can be so mischievous that he wants to maintain or persist the connection in the background without the knowledge of the user. This can be done using Trojans, Rootkits, or other malicious files. The aim is to maintain access to the target until he finishes the tasks he planned to accomplish in that target.
- Clearing Track:
No thief wants to get caught. An intelligent hacker always clears all evidence so that at a later point in time, no one will find any traces leading to him. This involves modifying/corrupting/deleting the values of Logs, modifying registry values and uninstalling all applications he used, and deleting all folders he created.
Introduction to Cryptography
Cryptography is the art of converting text into another form for secret transmission and reception. It works by converting plain text into cipher text using some encryption algorithm at the sender’s side and converting ciphertext into plain text at the receiver’s. Cryptography is used to provide confidentiality, integrity, authenticity, and non-repudiation.
Key terms:
Plain text: Message to be encrypted
Ciphertext: Encrypted message
Encryption: Process of converting plain text into cipher text.
Decryption: Process of converting ciphertext into plain text.
Algorithm: The method used to encrypt/decrypt the plain text.
Key: The data used for encrypting/decrypting.
There are various cryptographic algorithms present, generally, we categorize them as follows-
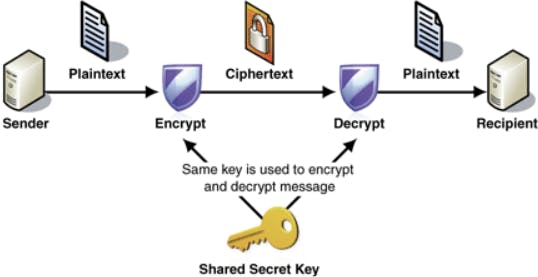
Symmetric cryptography:
Here one single key is used for encryption and the same key is used for decryption. DES and AES are examples of symmetric key cryptography.
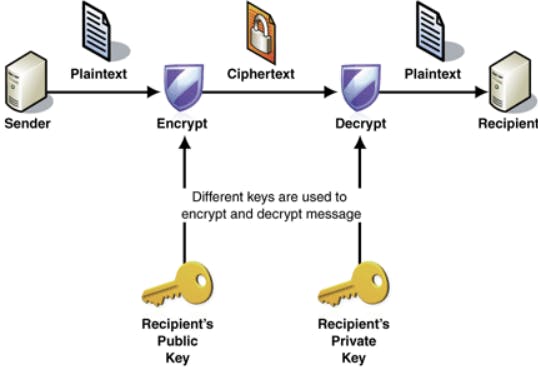
Asymmetric cryptography/Public key cryptography:
Here two keys are used, the Public key is used for encryption and the Private key is used for decryption; e.g. RSA.
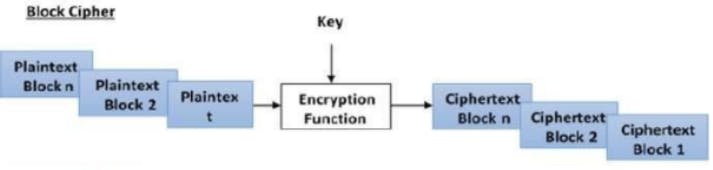
Block Cipher:
The input plain text is broken into fixed-size blocks and they are encrypted /decrypted as a block; e.g. DES, AES.
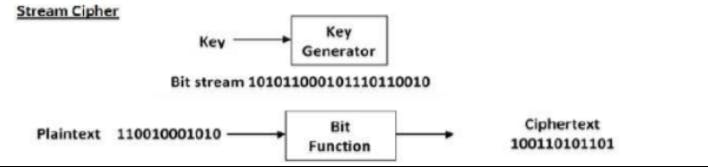
Stream cipher:
The incoming data is encrypted or decrypted byte by byte; e.g. RC4.
Digital Signatures:
Digital signatures are used to identify the genuinity of the source; the sender signs with his private key, and at the receiver’s end it can be decrypted only with the public key of the sender. This enables the receiver to know who has sent the message.
Hash Algorithms:
Hash algorithms are used to maintain the integrity of the data by finding a definite number for the file and verifying it at the receiver’s end.

At the sender’s side, the hash algorithm generates a fixed size number for the any-sized file. This number or hash value is sent along with the cipher text to the receiver. At the receiver’s end, the cipher text is first decrypted and then using a hash algorithm a hash value is generated. If the hash value matches the hash value that came with the cipher text, then the message was not corrupted. If it is different, then we can understand that the message has been intercepted and modified.
There are various hash algorithms
SHA1, SHA 256, MD5, etc.
Malware Analysis
The single term used for malicious software is malware. The malicious programs designed by cybercriminals can be collectively called malware. The malicious programs gain access to computing devices by creating a backdoor entry to steal personal information, confidential data, etc. Analysis of malware must be conducted to understand the types of malware, the nature of malware, and the attacking methodologies of malware, as malware attacks are increasing day by day. The process of analyzing and determining the purpose and functionality of the malware is called malware analysis. The information obtained by malware analysis can be used to develop techniques of detection for malware.

Stages of Malware Analysis
There are four stages of malware analysis. The stages are in the form of a pyramid and as we go higher in the pyramid, the complexity of the analysis stage increases. The stages are:
Assessment and Triage
The initial stage of malware analysis can be performed with the help of automation tools. For static analysis, some preparation steps are required, such as decompiling the code. Anyway, in the first stage of malware analysis, it’s necessary to sort out parts of the code that require close attention. They might also be divided into levels of difficulty and priority. After the scope of the malicious code to review is defined and prioritized, it’s time to move on to the next stage.
Data Interpretation
Next, Security Analysts get to examine specific malware samples. As I mentioned before, it can be done by analyzing the static properties or by running malware in a safe, isolated environment. When the Malware Analyst obtains all the data that can be exposed during static and dynamic analysis, they try to interpret what they see. They can further test the samples by renaming variables, running the code, and making comments about execution patterns.
Reverse Engineering
This is the most challenging part, especially if there’s an encrypted sample, and it’s unclear what it does and why. What’s more, the code might have multiple dependencies which are also not that obvious. Trying to reverse-engineer malware is an advanced task. Yet, it’s key to a Defense In Depth approach.
Conclusions & Further Actions
When the analysis findings are formulated, it’s time to document them and take further action. The Analyst writes a malware report where they describe a malware sample, stages of analysis that were taken, and conclusions. They can also give some remediation recommendations.

Tools for Malware Analysis
PeStudio is widely used by CERT teams worldwide for capturing artifacts of malicious files.
PEiD easily recognizes packed and encrypted malware and gives details about what it’s made of.
BinText is a text extractor that can find Ascii, Unicode, and Resource strings in a file.
MD5deep will calculate the malicious hashes. Used as a malware analyzer, this software package will run lots of files through various cryptographic digests.
Dependency walker will scan 32-bit or 64-bit Windows modules and create a dependency tree.
IDA Pro will disassemble the binary code into a source code. It also offers a cross-platform debugging capability that can handle remote applications.
When it comes to analyzing malware in sandboxes, you might have already tried Cuckoo, yet I’d recommend checking out ANY.RUN and Joe Sandbox Cloud. They both have MITRE ATTACK mapping, use rules, and give a very detailed view of behaviors.
Of course, Wireshark needs no introduction as it’s still one of the most widely used tools for real-time network analysis. INetSim realistically simulates internet services in a lab environment (the samples are highly unlikely to recognize the simulation). Then, there’s the Microsoft Sysinternals suite that I already mentioned above. You’ll find there a whole range of tools for dynamic malware analysis. ScyllaHide is another interesting tool that will let you hide a debugger from the malware that you want to run. And if you feel like doing a serious reverse-engineering project, check out Ghidra – a suite of tools developed by NSA’s Research Directorate.
Linux
Linux is an open-source operating system like other operating systems such as Microsoft Windows, Apple Mac OS, iOS, Google android, etc. An operating system is software that enables the communication between computer hardware and software. It conveys input to get processed by the processor and brings output to the hardware to display it. This is the basic function of an operating system. Although it performs many other important tasks, let's not talk about that.
Linux is around us since the mid-90s. It can be used from wristwatches to supercomputers. It is everywhere in our phones, laptops, PCs, cars, and even refrigerators. It is very much famous among developers and normal computer users.
Some of the basic Linux commands:
| Category | Requirements, Conventions or Software Version Used |
| System | Any Linux distro |
| Software | N/A |
| Other | Privileged access to your Linux system as root or via the sudo command. |
| Conventions | # – requires given linux commands to be executed with root privileges either directly as a root user or by use of sudo command |
$ – requires given linux commands to be executed as a regular non-privileged user |
File System Navigation
| Command | Description |
ls | List all the files in a directory |
ls -l | List all files and their details (owner, mtime, size, etc) |
ls -a | List all the files in a directory (including hidden files) |
pwd | Show the present working directory |
cd | Change directory to some other location |
file | View the type of any file |
View, Create, Edit, and Delete Files and Directories
| Command | Description |
mkdir | Create a new directory |
touch | Create a new, empty file, or update the modified time of an existing one |
cat > file | Create a new file with the text you type after |
cat file | View the contents of a file |
grep | View the contents of a file that match a pattern |
nano file | Open a file (or create new one) in nano text editor |
vim file | Open a file (or create new one) in vim text editor |
rm or rmdir | Remove a file or empty directory |
rm -r | Remove a directory that isn’t empty |
mv | Move or rename a file or directory |
cp | Copy a file or directory |
rsync | Synchronize the changes of one directory to another |
Search for Files and Directories
| Quickly find a file or directory that has been cached |
| Seach for a file or directory based on name and other parameters |
Basic Administration commands
| Command | Description |
whoami | See which user you are currently logged in as |
sudo | Execute a command with root permissions |
sudo apt install | Install a package on Debian based systems |
sudo dnf install | Install a package on Red Hat based systems |
sudo apt remove | Remove a package on Debian based systems |
sudo dnf remove | Remove a package on Red Hat based systems |
reboot | Reboot the system |
poweroff | Shut down the system |
- Hard drive and storage commands
| Command | Description |
df or df -h | See the current storage usage of mounted partitions |
sudo fdisk -l | See information for all attached storage devices |
du | See disk usage of a directory’s contents |
tree | View the directory structure for a path |
mount and umount | Mount and unmount a storage device or ISO file |
Compression Commands
| Command | Description |
tar cf my_dir.tar my_dir | Create an uncompressed tar archive |
tar cfz my_dir.tar my_dir | Create a tar archive with gzip compression |
gzip file | Compress a file with gzip compression |
tar xf file | Extract the contents of any type of tar archive |
gunzip file.gz | Decompress a file that has gzip compression |
Networking Commands
| Command | Description |
ip a | Show IP address and other information for all active interfaces |
ip r | Show IP address of default gateway |
cat /etc/resolv.conf | See what DNS servers your system is configured to use |
ping | Send a ping request to a network device |
traceroute | Trace the network path taken to a device |
ssh | Login to a remote device with SSH |
File Permissions and Ownership
| Command | Description |
chmod | Change the file permissions for a file or directory |
chown | Change the owner of a file or directory |
chgrp | Change the group of a file or directory |
User Management Commands
| Command | Description |
useradd | Low level utility for adding new user accounts |
adduser | High level utility for adding new user accounts |
deluser | Delete a user account |
usermod | Modify a user account |
groupadd | Create a new group |
delgroup | Delete a group |
System Resource Management Commands
| Command | Description |
free -m | See how much memory is in use and free |
top | See a list of processes and their resource usage |
htop | A more human readable and interactive version of top |
nice | Start a new process with a specified priority |
renice | Change the nice value of a currently running process |
ps aux OR ps -ef | View all of the currently running processes |
kill or killall | Terminate a process |
kill -9 or killall -9 | Terminate a process with SIGKILL signal |
bg | Send a task to the background |
fg | Bring a task to the foreground |
Environment Variable Commands
| Command | Description |
printenv or printenv variable_name | List all environment variables on a Linux system, or a specific one |
whereis and which | Find where a command in PATH is located |
export MY_SITE="linuxconfig.org" | Set a temporary environment variable (just an example, but use the same syntax) |
echo $VARIABLE | Display the value of a variable |
unset | Remove a variable |
Kernel Information and Module Management
| Command | Description |
uname -a | Output detailed information about your kernel version and architecture |
lsmod | Find what modules are currently loaded |
modinfo module_name | Get information about any particular module |
modprobe --remove module_name | Remove a module |
modprobe module_name | Load a module into the kernel |
Hardware Information Commands
| Command | Description |
lspci | See general information about host bridge, VGA controller, ethernet controller, USB controller, SATA controller, etc. |
dmidecode | See some information about BIOS, motherboard, chassis, etc. |
cat /proc/cpuinfo | Retrieve processor type, socket, speed, configured flags, etc. |
x86info or x86info -a | See information about the CPU |
cat /proc/meminfo | See detailed information about system RAM |
lshw | List all hardware components and see their configuration details |
lshw -C memory -short | Detect number of RAM slots used, speed, and size |
hwinfo | List details for all hardware, including their device files and configuration options |
biosdecode | Get some general information about your system’s BIOS |
dmidecode -s bios-vendor | Retrieve the name of your BIOS vendor with this simple command |
lsusb | Get a list of USB devices plugged into your system |
ls -la /dev/disk/by-id/usb-* | Retrieve a list of USB device files |
hdparm -I /dev/sdx | Get information about your hard drive’s make, model, serial number, firmware version, and configuration |
hdparm -tT /dev/sdx | Show the speed of an installed hard drive – including cached reads and buffered disk reads |
wodim --devices | Locate CD or DVD device file |
Basics of Networking
OSI stands for Open System Interconnection is a reference model that describes how information from a software application in one computer moves through a physical medium to the software application in another computer.
There are seven OSI layers. Each layer has different functions. A list of seven layers is given below:
Physical Layer
Data-Link Layer
Network Layer
Transport Layer
Session Layer
Presentation Layer
Application Layer
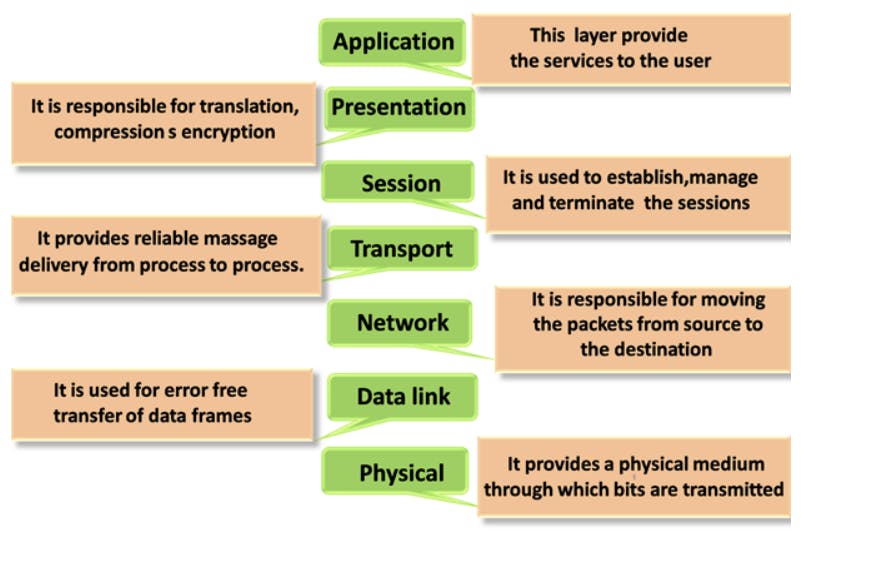
Application Layer
The application layer is the closest to the end user. It initiates communication between the user and the applications they personally interact with. At this layer, data is translated from the syntax it was converted to into something the user can read.
Examples of Layer 7 applications include a web browser like Chrome, Safari, or Firefox, or an email application. Layer 7 can also identify communication partners, check to see which resources are available, and make sure communication is properly synced.
Presentation Layer
The presentation layer takes care of getting data ready for the application layer. The two devices that are communicating may use different methods of encoding their data. Layer 6, therefore, turns the incoming data into something that can be read at the application layer. This includes encrypting and decrypting data.
The presentation layer also compresses data that comes from the application layer before it sends it on to Layer 5, the session layer.
Session Layer
The session layer handles opening and closing network communications between two interacting devices. The “session” refers to the time between the opening and closing of the interaction. The session layer makes sure the session is open for a long enough period of time for all the necessary data to be sent through. The session layer then closes the session to prevent expending unnecessary resources.
Also, it synchronizes the data transfer. If a large amount of data is being sent, the session layer can set up checkpoints. If the transmission gets interrupted before all the data is downloaded, the checkpoints allow the transmission to be resumed without it starting all over again.
Transport Layer
The transport layer handles end-to-end communication between the devices interacting with each other. The management of the communication involves taking the data in the session layer and dividing it into pieces referred to as segments. The transport layer on the device receiving the communication handles the reassembly of the segments into data that is consumable by the session layer.
Also, the transport layer takes care of managing the flow and any necessary error messages that need to be sent in the event something goes wrong. To manage data flow, the transport layer makes sure it is not being sent so quickly that the receiver’s device cannot handle it. To control errors, the transport layer checks to see if the data transmitted was done so completely. If it is not, this layer will request a retransmission.
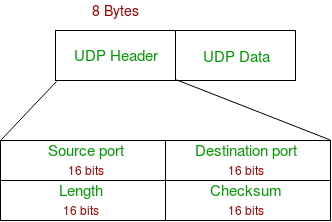
Layer 4 is where Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) port numbers work. Internet Protocol (IP) addresses operate at Layer 3, the network layer. TCP, UDP, and IP are protocols that facilitate how data is sent and received.
Network Layer
The network layer facilitates the transfer of data when two networks are communicating with each other. If two communicating devices are using the same network, then there is no need for the network layer. The network layer divides the segments that come from the transport layer. These are referred to as packets. The division of the segments into packets happens on the sender’s device, and they are reassembled on the receiving device.
The network layer also functions as an efficiency tool. It figures out the optimal physical path needed to get the data to its destination. This function is called “routing.”
Data Link Layer
The data link layer is like the network layer, except that the data link layer facilitates data transfer between two devices using the same network. In the data link layer, packets are broken into pieces referred to as frames. Similar to the network layer, the data link layer handles flow and error control. The transport layer is different in that it only manages the flow of data and errors when two networks are communicating with each other.
Within the data link layer, you have two sublayers, the media access control (MAC) and logical link control (LLC) layers. The majority of switches perform their duties at Layer 2. In some cases, switches work at Layer 3 because they are facilitating communication between two networks or virtual local-area networks (VLANs). This has to happen at Layer 3 because, in these situations, the data needs to be routed, which is a Layer 3 task.
Physical Layer
The physical layer involves the physical equipment that transfers data, like switches and cables. In this layer, the data is converted into strings of 1s and 0s. In the physical layer, the devices have to agree on a method of distinguishing the 1s from the 0s, which enables the digital data to be properly interpreted by each device.
The physical layer includes a variety of components, such as cables, the radio frequency used to transmit data, Wi-Fi, and other physical structures for transmitting data, such as pins, necessary voltages, and types of ports.


| TCP/IP | OSI Model | Protocols |
| Application Layer | Application Layer | DNS, DHCP, FTP, HTTPS, IMAP, LDAP, NTP,POP3, RTP, RTSP, SSH, SIP, SMTP, SNMP, Telnet, TFTP |
| Presentation Layer | JPEG, MIDI, MPEG, PICT, TIFF | |
| Session Layer | NetBIOS, NFS, PAP, SCP, SQL, ZIP | |
| Transport Layer | Transport Layer | TCP, UDP |
| Internet Layer | Network Layer | ICMP, IGMP, IPsec, IPv4, IPv6, IPX, RIP |
| Link Layer | Data Link Layer | ARP, ATM, CDP, FDDI, Frame Relay, HDLC, MPLS, PPP, STP, Token Ring |
| Physical Layer | Bluetooth, Ethernet, DSL, ISDN, 802.11 Wi-Fi |
Computer Network Protocols:
| Network Protocol | Description | Port number of protocol |
| Ethernet | A family of protocols that specify how devices on the same network segment format and transmit data. | 44818, 2222 |
| Wi-Fi or WLAN | A family of protocols that deal with wireless transmission. | – |
| TCP | Splits data into packets (reassembles later). Error checking is also included, as the acknowledgment is expected to be sent within a specified timeframe. | 22 |
| UDP | User Datagram Protocol | 4096-65535 |
| IP | Every device has an IP address. Packets are “addressed” to ensure they reach the correct user. | – |
| HTTP | Used to access web pages from a web server. | 80 |
| HTTP’S | uses encryption to protect data. | 443 |
| FTP | File Transfer Protocol: Handles file uploads and downloads, transferring data and programs. | 21 |
| SMTP | SMTP server has a database of user email addresses. Internet Message Access Protocol: Handles incoming mail. | 587 |
| IMAP | Internet Message Access Protocol: Process incoming mail. | 993 |
| ARP | ARP finds a host’s hardware address (also known as MAC (Media Access Control) address) based on its known IP address. | – |
| DNS | DNS is the host name for the IP address translation service. DNS is a distributed database implemented on a hierarchy of name servers. It is an application layer protocol for messaging between clients and servers. | 53 |
| FTPS | FTPS is known as FTP SSL which refers to File Transfer Protocol (FTP) over Secure Sockets Layer (SSL) which is more secure from FTP. FTPS also called as File Transfer Protocol Secure. | 21 |
| POP3 | POP3 is a simple protocol that only allows downloading messages from your Inbox to your local computer. | 110 |
| SIP | Session Initiation Protocol was designed by IETF and is described in RFC 3261. It’s the protocol of application layer that describes the way to found out Internet telephone calls, video conferences and other multimedia connections, manage them and terminate them. | 5060,5061 |
| SMB | The SMB protocol was developed by Microsoft for direct file sharing over local networks. | 139 |
| SNMP | SNMP is an application layer protocol that uses UDP port numbers 161/162. SNMP is also used to monitor networks, detect network errors, and sometimes configure remote devices. | 161 |
| SSH | SSH (Secure Shell) is the permissions used by the SSH protocol. That is, a cryptographic network protocol used to send encrypted data over a network. | 22 |
| VNC | VNC stands for Virtual Network Communication. | 5900 |
| RPC | Remote Procedure Call (RPC) is a powerful technique for building distributed client-server based applications. It is based on extending traditional calls to local procedures so that the called procedure does not have to be in the same address space as the calling procedure. | 1024 to 5000 |
| NFS | NFS uses file handles to uniquely identify the file or directory on which the current operation is being performed. Internet Control Message Protocol (ICMP) to provide error control. Used for reporting errors and administrative queries. | 2049 |
| ICMP | Internet Control Message Protocol(ICMP) to provide an error control. It is used for reporting errors and management queries. | – |
| BOOTP | Bootstrap Protocol (BOOTP) is a network protocol used by network management to assign IP addresses to each member of that network in order to join other network devices through a main server. | 67 |
| DHCP | Dynamic Host Configuration Protocol (DHCP) is an application layer protocol. DHCP is based on a client-server model, based on discoveries, offers, requests, and ACKs. | 68 |
| NAT | Network Address Translation (NAT) is the process of translating one or more local IP addresses into one or more global IP addresses, or vice versa, in order to provide Internet access to local hosts. | 5351 |
| PPP | Point-to-Point Protocol (PPP) is basically an asymmetric protocol suite for various connections or links without framing. H. Raw bit pipe. PPP also expects other protocols to establish connections, authenticate users, and carry network layer data as well. | 1994 |
| RIP | Routing Information Protocol (RIP) is a dynamic routing protocol that uses hop count as a routing metric to find the best path between source and destination networks. | 520 |
| OSPF | Open Shortest Path First (OSPF) is a link-state routing protocol used to find the best path between a source and destination router using its own shortest path first). | 89 |
| EIGRP | Enhanced Interior Gateway Routing Protocol (EIGRP) is a dynamic routing protocol used to find the best path and deliver packets between any two Layer 3 devices. | 88 |
| BGP | Border Gateway Protocol (BGP) is a protocol used to exchange Internet routing information and is used between ISPs in different ASes. | 179 |
| STP | Spanning Tree Protocol (STP) is used to create a loop-free network by monitoring the network, tracking all connections, and shutting down the least redundant connections. | 0 to 255 |
| RARP | RARP, stand for Reverse Address Resolution Protocol, is a computer network-based protocol used by client computers to request IP addresses from a gateway server’s Address Resolution Protocol table or cache. | – |
| LAPD | The D-channel LAPD or Link Access Protocol is basically the Layer 2 protocol normally required for the ISDN D-channel. It is derived from the LAPB (Link Access Protocol Balanced) protocol. | – |
| IPsec | IP Security (IPSec) is a standard suite of Internet Engineering Task Force (IETF) protocols between two communication points on IP networks to provide data authentication, integrity, and confidentiality. It also defines encrypted, decrypted, and authenticated packets. | 4500 |
| ASCII | ASCII (American Standard Code for Information Interchange) is the standard character encoding used in telecommunications. The ASCII representation “ask-ee” is strictly a 7-bit code based on the English alphabet. ASCII codes are used to represent alphanumeric data. | 9500 |
| EBCDIC | EBCDIC (Extended Binary Encoded Decimal Interchange Code) (pronounced “ehb-suh-dik” or “ehb-kuh-dik”) is an alphanumeric binary code developed by IBM to run large-scale computer systems . | – |
| X.25 PAD | X.25 is an International Telecommunication Union Telecommunication Standardization Sector (ITU-T) protocol standard simply for Wide Area Network (WAN) communications that basically describes how the connections among user devices and network devices are established and maintained. | – |
| HDLC | High-Level Data Link Control (HDLC) commonly uses the term “frame” to denote units or logs of units of data that are frequently transmitted or transmitted from one station to another, express. Each frame on the link must start and end with a flag sequence field (F). | – |
| SLIP | SLIP stands for Serial Line Internet Protocol. It is a TCP/IP implementation which was described under RFC 1055 (Request for Comments). | |
| LAP | Link Access Procedure (LAP) is basically considered as an ITU family of Data Link Layer (DLL) protocols that are subsets of High-Level Data Link Control (HDLC). LAP is particularly derived from IBM’s System Development Life Cycle (SDLC). | – |
| NCP | Network Control Protocol (NCP) is a set of protocols that are part of Point-to-Point Protocol (PPP). | 524 |
| Mobile IP | Mobile IP is a communication protocol (created by extending the Internet Protocol, IP) that allows a user to move from one network to another using the same her IP address. | 434 |
| VOIP | Voice over Internet Protocol (VoIP), is a technology that allowing you to make voice calls over a broadband Internet connection instead of an analog (regular) phone line. Some VoIP services allow you to call people using the same service, but others may allow you to call anyone. | 5060 |
| LDAP | Lightweight Directory Access Protocol (LDAP) is an internet protocol works on TCP/IP, used to access information from directories. LDAP protocol is basically used to access an active directory. | 389 |
| GRE | GRE or Generic Routing Encapsulation is a tunneling protocol developed by Cisco. It encapsulates IP packets i.e. deliverable inner packets into outer packets. | 47 |
| AH | The HTTP headers Authorization header is a request type header that used to contains the credentials information to authenticate a user through a server. If the server responds with 401 Unauthorized and the WWW-Authenticate header not usually. | 51 |
| ESP | Encapsulation security payload, also abbreviated as ESP plays a very important role in network security. ESP or Encapsulation security payload is an individual protocol in IPSec. | 500 |
| NNTP | Network News Transfer Protocol (NNTP) is the underlying protocol of UseNet, which is a worldwide discussion system which contains posts or articles which are known as news. | 119 |
| RPC-DCOM | DCOM- Distributed Component Object Model– helps remote object via running on a protocol known as the Object Remote Procedure Call (ORPC). | – |
| IRC | Internet Relay Chat (IRC) is an Internet application that was developed by Jakko Oikarinen in Finland. Chat is the most convenient immediate way to communicate with others via Internet. | 6667 |
Networking Devices:
| Device | Description |
| Client | Any device, such as a workstation, laptop, tablet, or smartphone, that is used to access a network. |
| Server | Provides resources to network users, including email, web pages, or files. |
| Hub | A Layer 1 device that does not perform any inspection of traffic. A hub simply receives traffic in a port and repeats that traffic out of all the other ports. |
| Switch | A Layer 2 device that makes its forwarding decisions based on the destination Media Access Control (MAC) address. A switch learns which devices reside off which ports by examining the source MAC address. The switch then forwards traffic only to the appropriate port, and not to all the other ports. |
| Router | A Layer 3 device that makes forwarding decisions based on Internet Protocol (IP) addressing. Based on the routing table, the router intelligently forwards the traffic out of the appropriate interface. |
| Multilayer switch | Can operate at both Layer 2 and Layer 3. Also called a Layer 3 switch, a multilayer switch is a high-performance device that can switch traffic within the LAN and for- ward packets between subnets. |
| Media | Media can be copper cabling, fiber-optic cabling, or radio waves. Media varies in its cost, bandwidth capacity, and distance limitation. |
| Analog modem | Modem is short for modulator/demodulator. An analog modem converts the digital signals generated by a computer into analog signals that can travel over conventional phone lines. |
| Broadband modem | A digital modem used with high-speed DSL or cable Internet service. Both operate in a similar manner to the analog modem, but use higher broadband frequencies and transmission speeds. |
| Access point (AP) | A network device with a built-in antenna, transmitter, and adapter that provides a connection point between WLANs and a wired Ethernet LAN. APs usually have several wired RJ-45 ports to support LAN clients. Most small office or home office (SOHO) routers integrate an AP. |
Classes in Computer Networking:
| CLASS | LEADING BITS | NET ID BITS | HOST ID BITS | NO. OF NETWORKS | ADDRESSES PER NETWORK | START ADDRESS | END ADDRESS |
| CLASS A | 0 | 8 | 24 | 27 ( 128) | 24 2 (16,777,216) | 0.0.0.0 | 127.255.255.255 |
| CLASS B | 10 | 16 | 16 | 14 2 (16,384) | 16 2 (65,536) | 128.0.0.0 | 191.255.255.255 |
| CLASS C | 110 | 24 | 8 | 21 2 (2,097,152) | 8 2 (256) | 192.0.0.0 | 223.255.255.255 |
| CLASS D | 1110 | NOT DEFINED | NOT DEFINED | NOT DEFINED | NOT DEFINED | 224.0.0.0 | 239.255.255.255 |
| CLASS E | 1111 | NOT DEFINED | NOT DEFINED | NOT DEFINED | NOT DEFINED | 240.0.0.0 | 255.255.255.255 |
Methods of Network Security:
| Method | Description |
| Authentication | Verify a user’s identity, usually by asking them to enter a password or biometric identifier. |
| Encryption | Encrypt data with a key, that is, the same key is required to decrypt the data. This is how HTTPS works. |
| Firewalls | Protect the network from unauthorized access. |
| MAC Address Filtering | Allow devices to access or be prevented from accessing the network based on their physical address embedded in the device’s network adapter. |
Fields in Cybersecurity
There are various paths to take in Cybersecurity, all of which have different areas of specialization. Some of the fields include:
Application Security
Penetration Testing
Reverse Engineering
Digital Forensic Analysis
Systems Administration
Malware Analysis
Cryptography
Common Cybersecurity Certifications
Certified Ethical Hacker (CEH)
CompTIA Security+
Certified Information System Security Professional (CISSP)
Certified Information Security Manager (CISM)
Certified Information Systems Auditor (CISA)
NIST Cybersecurity Framework (NCSF)
Certified Cloud Security Professional (CCSP)
Computer Hacking Forensic Investigator (CHFI)
Cisco Certified Network Associate (CCNA) Security
Why learn Cybersecurity?
You're learning and building a skill that only a tiny percentage of people have.
High demand for cybersecurity experts.
Cybersecurity is an evergreen industry where personnel is needed in every single company operating in the digital space.
Unlimited career growth options.
Opportunities to work with high-profile agencies.
It's filled with a lot of fun and exciting moments.
Lots of children break things not because they are little evil creatures but because they are curious about “how it’s made.” Eventually, some of those children grow up and become Cybersecurity Analysts. They do basically the same but in an adult world. This has been useful in my project, where I've had the opportunity to work on real-world problems and apply my knowledge to practical scenarios.
Along with the technical stuff, we had a few fun activities where we shared one random yet amazing fact twice a week. Every time we got amazed by the fact and research about what exactly it is, every time it turns out to be simple stuff that our subconscious mind had made us forget about it. We even read one self-help book every month and discovered a simple habit to add to our daily routine which has made a drastic change in our life.
One of the most valuable things I've gained is a better understanding of how to think like an attacker. By learning about the tactics and techniques that hackers use, I've been able to develop a mindset that allows me to anticipate and defend against potential threats.
Conclusion
Overall, my journey into cybersecurity as a developer in Celestial Biscuit has been challenging but rewarding. I've learned a lot and gained valuable skills that I know will be useful in my career. If you're considering a career in cybersecurity, I highly recommend it. It's a dynamic and growing field with plenty of opportunities for those who are passionate about keeping organizations and individuals safe online.
In this article, we walked through the prerequisites of Cybersecurity and saw what is security, OWASP, cyber threats, forms of Cyber Threats, and techniques of cyber attacks. We also explored the phases of hacking, cryptography, malware analysis, stages of malware analysis, and tools used in the analysis. We took a deep dive into Linux, basic commands of Linux, basics of networking, looked at a couple of Cybersecurity certifications, and why people should have Cybersecurity skills.
I also plan to start a series that goes in-depth into explaining each topic of forms of cyber-attacks, how they are carried out, and show how to protect your application from them. Subscribe, so you don't miss out on this.
